Kubernetes Myth #08: Kubelet runs only on worker nodes!
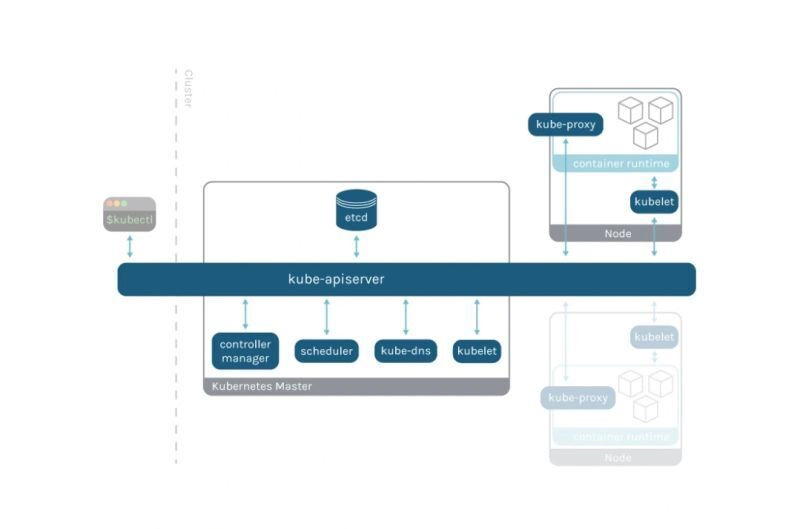
🧐 If Kubelet is only for worker nodes, then who runs the control plane components like the API server, scheduler, and controller-manager?Reality: ❌ Kubelet runs on both worker and control plane n...