What are the common methods to prevent unauthorized access to FPGA designs?
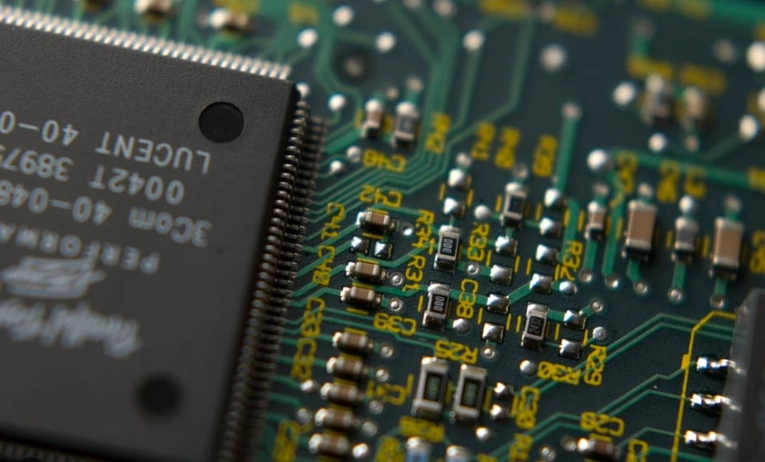
FPGAs are often used in sensitive applications (e.g., defense, finance, IoT), making security critical. Below are key techniques to protect FPGA designs from unauthorized access, reverse engineering, ...